Unlocking the DFIR Job Market: Strategies for Landing Your Dream Role
tl;dr: This blog aims to aggregate what I’ve found meaningful while job hunting in my career, and to be a useful resource to anyone interested in a career in DFIR. If you don’t care what I think, skip to the bottom for people who said it better than me.
I’ve been thinking about and talking to a lot of early-career professionals recently and wanted to document some of the discussions we’ve had. A lot of people seem lost; they want a career in cybersecurity but don’t really know where to start.
It can be difficult when there are so many different roles and job titles and little standardisation. The requirements for a role can differ vastly depending on the hiring manager and the HR team (not to call anyone out; it’s a fast-moving field and it’s hard to keep up). There’s no shortage of advice like this; I realise of course that a quick Google search brings up a multitude of similar blogs, but if people are still asking “where do I start”, at least having written this I have somewhere to point them for a quick rundown of my thoughts.
A quick word on job opportunities generally before we get into the material proper: I don’t have much experience with the job market in the US or the EU so I can’t comment with authority on the level of demand for cybersecurity professionals, much less which types of cybersecurity professionals are most needed. However, cybersecurity is a growing industry and that isn’t going to change. Cybersecurity is a global industry and companies everywhere are becoming more aware of the need to protect their assets from adversaries, so the job market will continue to trend up globally.
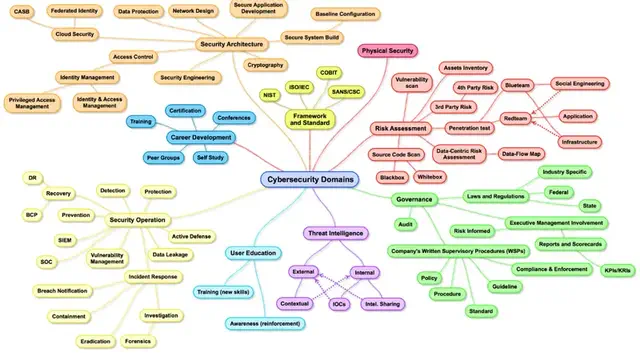
Cybersecurity Career Paths
Reference: Cybersecurity Domain Map ver 3.0
There are so many jobs and job titles in cybersecurity now that separating and filtering them can be challenging. My background is in digital forensics and incident response (DFIR), so this post will be slanted that way. There’ll be overlap in other areas, I’m sure.
DFIR is an area of cybersecurity that focuses on investigating and responding to security breaches and incidents. DFIR professionals use various techniques and tools to identify the source (or root cause) of a security incident, collect evidence, and prevent future attacks.
DFIR Careers
There are several different types of roles within DFIR, including (in what I think is order of seniority):
Network and Systems Administrator (where I started)
These are the people responsible for the day-to-day operations of a network and its endpoints. They design, install, configure, and maintain networks and systems, and then monitor, troubleshoot, and optimise network performance, ensuring high availability and security.
SOC Analyst
Monitor network traffic and security logs to identify potential security incidents, then investigate and respond to security events, performing analysis and providing recommendations for remediation. The SOC can also perform vulnerability assessments and manage security systems, like firewalls, IDS/IPS, and SIEM. In most cases, the SOC will hand off to a specialist incident response team when things get too sophisticated.
Forensic Examiner
Responsible for conducting investigations into cybercrime, meaning this title is usually used by law enforcement and less so in the broader community (in my experience). They collect and analyse digital evidence, prepare reports, and present findings in court.
Digital Forensic Analyst
Responsible for identifying and collecting digital evidence related to a security incident. Must have a deep understanding of computer systems, networks, and digital storage media. The difference here is that digital forensic analysts are usually outside of law enforcement, working for consultancies or internal forensics teams at large organisations.
Incident Responder / DFIR Consultant / IR Consultant
Responsible for responding to and managing security incidents as they occur. Must be able to quickly identify the nature of an incident, contain it, and develop a plan to mitigate the damage. Can be part of an internal or managed SOC. Usually part of a consultancy or more mature large organisation.
Other Career Paths
Outside of DFIR, there are a lot of other really interesting roles as well:
Malware Analyst
Responsible for identifying and then analysing malware in an environment. Must be able to reverse engineer malware to understand how it works and develop tools to defend against it.
Penetration Tester
Conduct controlled, sanctioned attacks on systems, networks, and applications to identify vulnerabilities and weaknesses so they can document findings and provide recommendations for remediation to stakeholders, closing gaps in security.
Threat Intelligence Analyst
Monitor and analyse threats to identify potential security incidents or risks. Threat intel teams collect and analyse threat intelligence data from multiple sources to develop and maintain threat intelligence reports, providing recommendations to stakeholders.
Examples of the threats an analyst might be interested in are available from several organisations and service providers:
Skills Needed for Any of These Roles
In terms of the particular skills required, it really depends on whether you want to be a security generalist or a specialist. Each of these areas lends itself to certain personality types, traits, and skillsets.
If your interest lies in digital forensics, find learning material online (YouTube is a great place to start, and then Cybrary, Udemy, or any of several other online academies). Alternatively, capture-the-flag (CTF) contests can build those skills, and commercial classes can accelerate you (which I’ll delve into later).
If you’re interested in incident response, look for materials and exercises that focus on those skills, and understand that you need to be the kind of person who thrives under pressure and is able to stay calm in the face of adversity (from all angles, adversary and client alike).
Understand that there are many other specialties; it’s just that these two are mine so I feel comfortable speaking about them.
The Day-to-Day of DFIR
In addition to the skills needed for any specialty, you’ll likely need other skills (depending on the company you work for). As an incident response consultant, for example, client engagements won’t always be incidents. A lot of the time it’ll be proactive work, like architecture reviews, tabletop exercises, IR plan/playbook development workshops, etc.
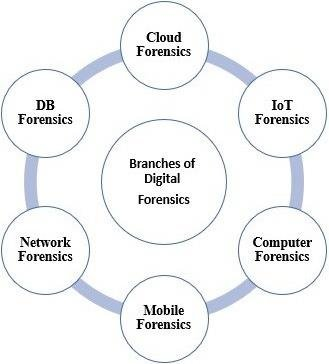
Having a really good grounding in at least one of network, memory, or disk forensics is necessary (my background is heavily in disk but any of the three is useful). If you can program or script, that’s a bonus. Outreach is important too, so being interested in writing blogs, whitepapers, and submitting to CFPs is a nice-to-have, but not a requirement.
Besides that, it’s experience and being able to communicate effectively to audiences of different technical ability. If you can help a client go from preparation and detection through to remediation, you’ve probably got the right skillset.
Other Roles in Cybersecurity
I’m probably missing someone, but this is a reasonable list of the jobs available in cybersecurity (excluding risk management and GRC, which I’m not super familiar with).
If any of these interest you, do your own research to figure out where your skill set matches up, and your personality (for example: if you work well under pressure and tend to keep calm, incident response might be a good choice; otherwise, maybe not so much).
Once you’ve decided which role makes the most sense, it’s time to brush up that resume.
Sell Yourself: Crafting Your Resume
Your resume is your sales pitch. As such, preparing a strong one is critical when applying for jobs in any field, but definitely DFIR.
Use Google’s “X-Y-Z” Model
This model emphasises results and impact over responsibilities. Rather than listing your job duties or copy-pasting your job description, focus on specific accomplishments and achievements.
You have 3–5 bullet points to highlight quantifiable results, such as:
- “Reduced incident response time by 50% using automation, resulting in 100% YoY retainer growth.”
- “Identified and removed over 1,000 instances of malware by implementing new processes for more than 50 clients.”
NB: Obviously these are contrived, but you get the idea: achieved x by doing y, resulting in z.
Use Action Words to Describe Your Accomplishments
Starting each bullet point with a verb makes your achievements sound more impactful and engaging. For example, instead of writing “Responsibilities included monitoring network traffic,” write “Monitored network traffic to identify and prevent potential security breaches, resulting in fewer false positives.”
Keep it Concise
Your resume should be no more than two pages. Be selective about what you include and focus on the most relevant and impressive achievements. Use a clear, easy-to-read font, and keep formatting consistent throughout.
Use LinkedIn to Supplement Your Resume
LinkedIn is a powerful tool. It enables you to showcase your professional experience and connect with potential employers.
Use your LinkedIn profile to provide additional detail on your work experience and accomplishments.
Be Prepared to Speak to Anything on Your Resume
If it’s on your resume, you must be prepared to provide more detail if asked. Make sure you can speak confidently about your achievements and answer any questions the interviewer may have. If you find that challenging, consider replacing or removing that item.
Skip the Career Objective and Other Exposition
Career objectives are unnecessary and take up valuable space (I used to have one, but since reviewing several resumes, I’ve discovered I never read them).
Instead, use the limited space to highlight your key strengths and accomplishments and your tenure in each role (start/end date; at least the year, but the month helps, too).
The main thing is making sure your resume is up to date and tailored for the role for which you’re applying. Tailor it to the job because each posting is unique, so your resume should fit the specific requirements of that position. Highlight the skills and experiences most relevant to the job description and use similar language to that used in the posting.
A strong resume, in my experience, is results oriented. Keep it concise, use the X-Y-Z model, and be prepared to speak to anything on your resume during interviews.
For an example of a really not good resume, check out Lesley’s blog: The Worst InfoSec Resume, Ever
Invest in Your Resume
While it’s certainly possible to create a strong resume on your own, using a professional resume writing service can provide significant benefits.
Just like everyone should have a mental health professional, everyone should consider using a professional resume writing service to help them achieve their career goals.
Professional resume writers are skilled in crafting resumes tailored to the specific needs of each client. They know what hiring managers and recruiters are looking for and can help you highlight your strengths and accomplishments in a way that catches attention.
Admittedly, a good resume writing service isn’t cheap, but it can be a valuable investment in your career. When considering the cost, think about the potential return on investment. If a professional resume helps you land a role with a salary that’s $10,000 higher than your current position, the ROI is significant when that increased remuneration compounds year after year.
Do your homework: look for a company with a proven track record of success. Check reviews, testimonials, and samples (where possible) from previous clients to get a sense of their expertise. Make sure the service includes a consultation with a professional writer, so you can collaborate on creating a resume that reflects your unique skills and experience.
Stand out: Non-work Experience
In addition to work experience, there are several activities you can pursue to enhance your skills and stand out while job hunting in DFIR.
Build a Home Lab
Setting up a home lab is a great way to gain hands-on experience with different tools and techniques. There are other articles on this blog to help you do that, or you could look at the book as a guide:
Reference: Cybersecurity for Small Networks
Collaboration on Git and Open-source Projects
Creating and working on your own or collaborating with others on open-source projects via platforms like GitHub can help you build your network and demonstrate your skills to potential employers.
Write Your Own Security Research Blog
Writing a blog focused on security research can be a great way to showcase your expertise and insights. By sharing your research and analysis with others, you can build your personal brand and establish yourself as a thought leader in the field.
I might cover this in a later blog, but it’s not necessary to generate novel research (that’s a bonus); it’s perfectly reasonable to cover research that’s been done before and approach it from a new angle or perspective.
This isn’t just for employment opportunities, but for your own reference as well. A good way to approach it if you struggle for ideas (like I do) is to participate in or complete CTFs and then write up your process and findings.
Complete Training and Get Certified
There are so many training programs and certifications available in DFIR, and obtaining these creds can demonstrate your commitment to continuous learning and professional development.
Examples of popular certs include the GIAC Certified Incident Handler (GCIH) from SANS, and the Certified Computer Forensic Examiner (CFCE) from IACIS.
If SANS is of interest to you, check out my other blog on getting SANS certified: A Roadmap to Earning Your First (or next) SANS Certification
In my experience, certifications are most helpful for job hunters who have little experience in the field. If you’re someone with 3–5+ years’ experience, there’s a law of diminishing returns that applies after a certain point, and getting more certs isn’t as helpful anymore.
GIAC/SANS are the certifications that most hiring managers focus on in cybersecurity, although certifications like the OSCP, CISSP, and others are also looked upon favourably.
NB: CISSP is favoured more by HR than by practitioners, more as a gatekeeping mechanism; the cert itself provides little practical value, in my opinion.
Using tools and services like Blue Team Labs Online and HacktheBox is another great way to gain experience and show competency:
Community Outreach: Engagement via Presentations and CFPs
Getting involved in the DFIR community can help you build your network and establish yourself as a leader in the field. Consider submitting proposals to speak at conferences or events, or volunteering to lead a workshop or training session. This can help you build your reputation and gain valuable experience in public speaking and community outreach.
By pursuing these non-work experience value adds, you can demonstrate your passion and commitment to the DFIR field while also building your skills and network.
When interviewing for jobs, highlight any relevant experience or accomplishments, whether they come from work or non-work activities.
Company Research Can Set You Apart
Before attending your interview (possibly even before applying to a company), you have to do your homework and research them. Here’s why:
- Understand the company’s mission and values. This can help you tailor your responses to align with their goals and culture.
- Familiarise yourself with the company’s products or services. This enables you to demonstrate your interest in their work and provide insight into how you can contribute.
- Research the company’s or interviewers’ recent news or accomplishments to identify discussion points or areas of mutual interest.
Demonstrating your knowledge and interest can set you apart and show commitment to the role. Researching the company helps you prepare targeted questions for the interviewer.
Check out the company’s social media channels and blog to see what topics they care about. Understand the company’s competition and industry trends.

For example, when I applied to Dragos, I looked at all the material I could to get a leg up. Luckily, they put out a lot, so there was plenty available. I was able to watch their YouTube videos to get an understanding of how they worked, what they were interested in, which frameworks they referred to, and the company culture.
I was able to reference their blogs and whitepapers during the interview process, all of which added to my eventual pitch for myself as a potential hire.
By doing your homework, you’ll be better equipped to showcase your skills and experience in the context of the company’s needs and goals. You’ll also be better prepared for the conversation you’ll have and the questions you’ll likely be asked.
If you can, reach out to a few employees ahead of time and ask for their opinions on the company and the role.
Common Cybersecurity Interview Questions (and how to respond)
Honestly, if you’ve ever gone to an interview without having some idea of the questions you’ll be asked, what are you even doing searching for a job. If you go in completely cold, you’re making it harder than it needs to be.
My point is: there’s so much information available online (practice questions, interview classes and workshops, flash cards, mentorship programs…) that you should be prepared for at least the most commonly asked questions, at least in a broad sense. I’ve captured a few of those here:
Tell me about yourself
This open-ended question often catches people off guard, and it really shouldn’t because it’s almost always the first question you’ll be asked. This is an opportunity to sell yourself. Focus on your experience, strengths, and your passion for cybersecurity.
Don’t go all the way back to the beginning of time; it’s usually best to focus on the last ~10 years at most, with the most focus being on the last 3–5 years. Develop a short 30 - 45 second elevator pitch to cover where you’ve been and what you’ve done.
Why do you want a career in cybersecurity?
Designed to test your motivation and enthusiasm for the field. It sounds a bit trite, but it’s a common question. Be honest, show some personality, and highlight any personal experiences that sparked your interest.
Alternative: What’s your understanding of cybersecurity, and why do you want to work in this field?
Tests your understanding of the field and your motivation. A good answer highlights the importance of cybersecurity and your interest in protecting organisations and individuals from threats. Even better if you can name and talk about a specific breach or incident.
What are your strengths and weaknesses?
Be honest but focus on your strengths, and explain how you’re working to improve any weaknesses. Avoid statements like “I work too hard, I care too much.” Chances are they’ve heard it all before, so just be honest.
What are your favourite cybersecurity tools?
This is one of those times you’ll be speaking about the things on your resume. Be prepared to discuss your experience with common tools and why you prefer them.
For example, I prefer X-Ways over EnCase; it’s objectively superior for several reasons, but mostly because the functionality is greater in several ways. If you’re interviewing at an EnCase shop, make sure you have facts to back up your arguments.
Also, if you list KAPE, FTK, Velociraptor, Elastic Stack, or any specific tools on your resume, be prepared to discuss them in depth.
Alternative: What tools and technologies are you familiar with in the cybersecurity space?
Again, tests your knowledge and experience. A strong answer would demonstrate familiarity with common tools such as SIEMs, forensic suites like SIFT, The Sleuth Kit, AXIOM, X-Ways, vulnerability scanners — and highlight how you’ve used them.
Tell me about a time you faced a challenging client and how you overcame it.
Designed to figure out how you handle pressure and difficult situations. Use the STAR method (Situation, Task, Action, Result) to structure your response, and focus on the steps you took (or would take) to resolve the issue.
Alternative: Tell me about a time you failed and how you recovered or turned that into something positive.
Tests resilience and problem-solving. Everyone’s failed at some point; don’t pretend you haven’t. Own it and explain what you learned and how you improved.
What are the different types of cyber-attacks, and how would you defend against them?
Assesses your technical knowledge and ability to articulate defence mechanisms. A strong answer demonstrates understanding of different attacks (phishing, malware, DDoS) and how you’d defend against them. Bonus points if you can reference a well-known incident.
Can you walk me through a recent security incident / case / engagement you worked on and how you resolved it?
Evaluates real-world experience and problem-solving. Describe a specific incident, the steps you took, and the outcome.
- How do you stay up to date on the latest cybersecurity threats and trends?
Assesses commitment to professional development. A good answer covers industry associations, conferences / webinars, and engagement with relevant blogs and podcasts.
- How do you prioritise cybersecurity risks within an organisation?
Evaluates strategic thinking. Describe a risk assessment process and how you weigh impact, likelihood, business context, and compliance.
- Can you describe your experience working with cross-functional teams on cybersecurity initiatives?
Tests collaboration with stakeholders (IT, legal, compliance, etc.). Give examples of projects where you aligned people with different priorities.
Just for fun, here’s a quote from Lesley Carhart on professional curiosity:
“What divides an ‘okay’ information security candidate from a great one is the motivation to learn more about the field outside work, every week,” she said. “What this looks like depends on [your] niche — perhaps working in a home lab or reading new computer legislation.” … “Regardless, people who have no interest in the field outside of business hours will quickly find themselves at a disadvantage in the market,” she said.
Reference: Landing that infosec job: These experts share their best career advice
“I Don’t Know” 🤷
If you don’t know the answer to a question, it’s better to say “I don’t know” than to guess or make something up, in almost all situations (not just interviews).
It’s perfectly reasonable not to know something, like the port DNS uses (UDP 53), or whether a decryptor exists for a specific ransomware family. If you’re not sure, say so, then explain how you’d verify it.
Alternatively, make it known that you’re not sure, but you’ll take a stab at it, then reason it out. Using logic to arrive at a conclusion (even if it’s not exactly correct) demonstrates that you can think clearly under pressure.
Levels or Years of Experience
The more years of experience you have, the more depth your interviewer is likely to expect. I don’t expect the same breadth from someone applying for a junior position as I do for someone gunning for a Principal or Director role.
Overall, with the number of resources available via a quick search, there’s no excuse for being unprepared to articulate your technical skills, experience, and soft skills (communication and collaboration) during interviews.
You should also be able to provide specific examples and anecdotes that demonstrate your ability to tackle real-world cybersecurity challenges.
Asking Questions
You must ask questions at the end of the interview. If you don’t, you’ll seem disinterested or unprepared. Have a couple of questions ready:
What qualities do successful employees in this team / role need to have?
Shows you’re interested in what the company values and helps you assess fit (the interview goes both ways).
What do you see as the most challenging aspect of this position?
Demonstrates you’re willing to tackle challenges and helps surface red flags early.
What are the opportunities for professional development within the company?
This one can be tricky; read the room. It can sound like you’re only interested in perks. On the plus side, if that’s how it’s received, you may not want to work there anyway.
What do you like best about working for this company? (Or: why do you work here?)
This often disarms people (not by design) and can reveal a lot about culture.
What’s the next step in the interview process?
Always good to know where you stand.
Again: don’t waste the opportunity to ask questions. You might gain insight into the process, and it’s another chance to help them decide you’re the candidate they want.
Fundamentals: Key Concepts Every DFIR Professional Should Know
Here’s a selection of the concepts and frameworks that I’d recommend anyone in cybersecurity be familiar with. All models are wrong, but some are useful. I’d count these as useful.
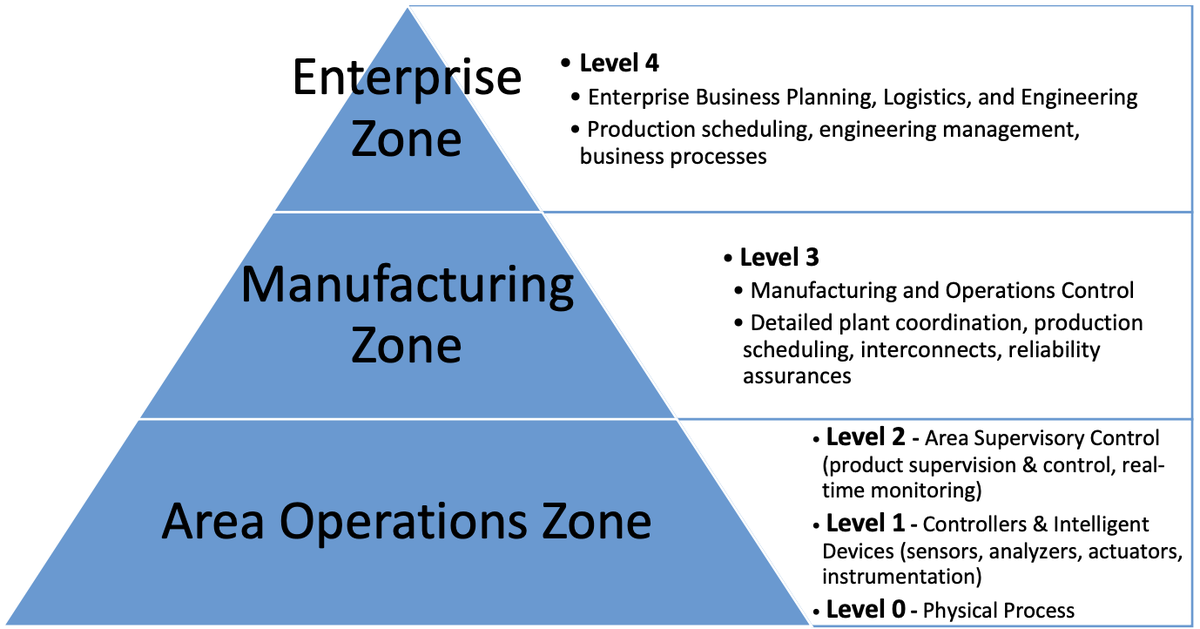
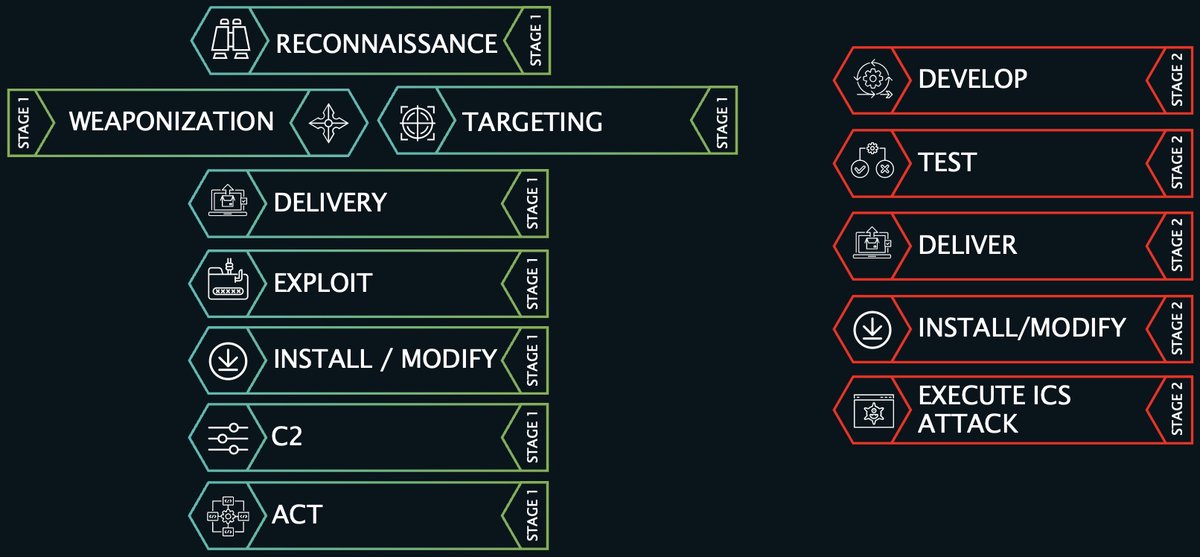
NB: to be fair, Purdue Model and ICS Cyber Kill Chain are niche and specific to ICS/OT. But the original kill chain is worth knowing, so by extension so is the ICS version. Purdue is just interesting, even if you’re not in industrial environments day-to-day.
Purdue Model
The Purdue Model is a hierarchical model used to describe the flow of data through an industrial control system. It can be helpful for identifying potential cybersecurity gaps and implementing risk-mitigating architectural controls.
ICS Cyber Kill Chain
A lot of us are familiar with the original Lockheed Martin Cyber Kill Chain: a model designed for IT environments that shows the steps an adversary must pass through to achieve actions on objectives.
The ICS version is designed for industrial control system environments, outlining stages of an ICS cyber-attack and providing guidance on how to detect and respond.
References:
MITRE ATT&CK
A knowledge base of adversary tactics, techniques, and procedures (TTPs) based on real-world observations.
ATT&CK for ICS is an extension designed for ICS/OT environments and aims to provide a similar framework for understanding threats and assisting defenders in detecting and mitigating attacks.

Reference: MITRE ATT&CK Framework: Everything You Need to Know
The Sliding Scale of Cybersecurity
A model used to evaluate an organisation’s cybersecurity posture, considering the specific risks and threats faced, and providing guidance on how to improve posture. I use it at home, too.
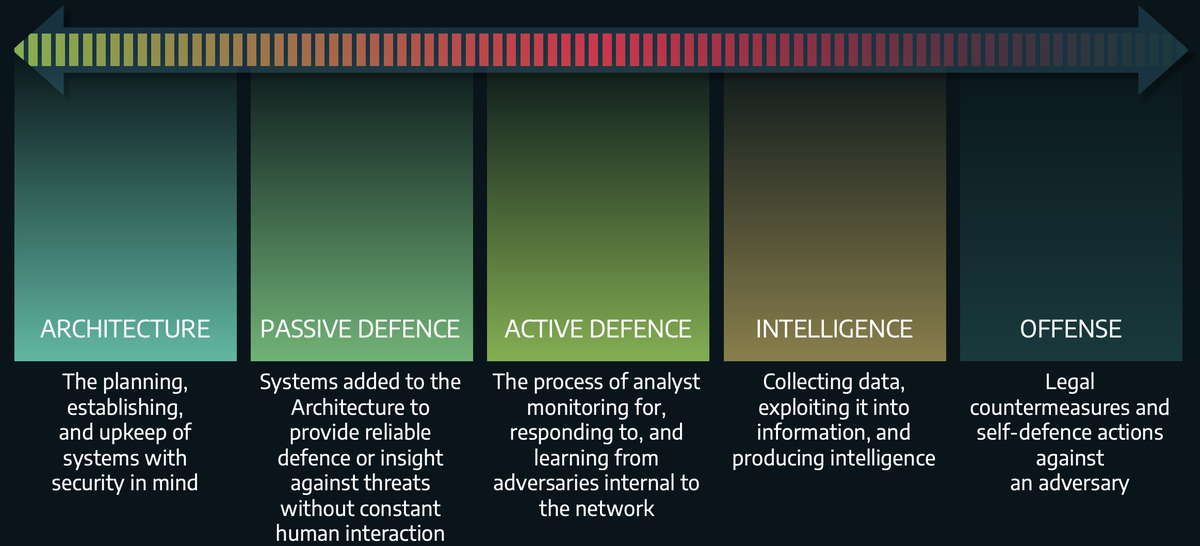
Reference: The Sliding Scale of Cyber Security
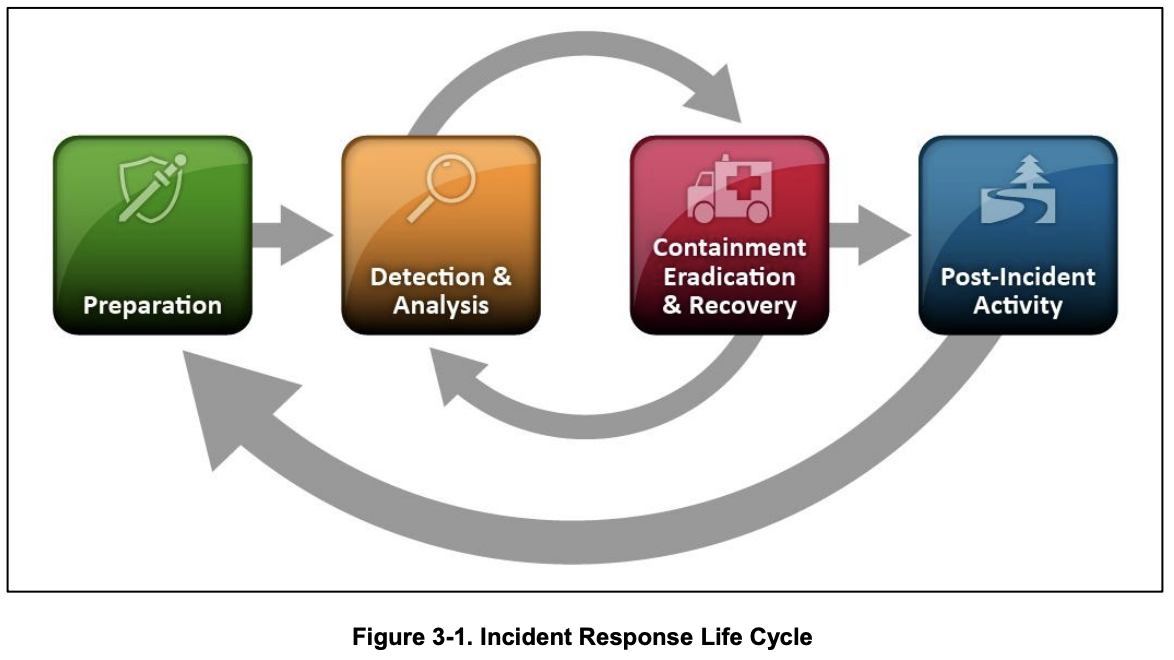
NIST IR Lifecycle / PICERL
The NIST Incident Response Lifecycle (often mapped to PICERL language) is a framework for incident response, outlining the steps you take before, during, and after an incident.
References:
The Diamond Model for Intrusion Analysis
A model used for intrusion analysis incorporating four key elements: threat actor, infrastructure, capability, and victim. Using all four can help build a more detailed understanding of an attack and inform response measures.
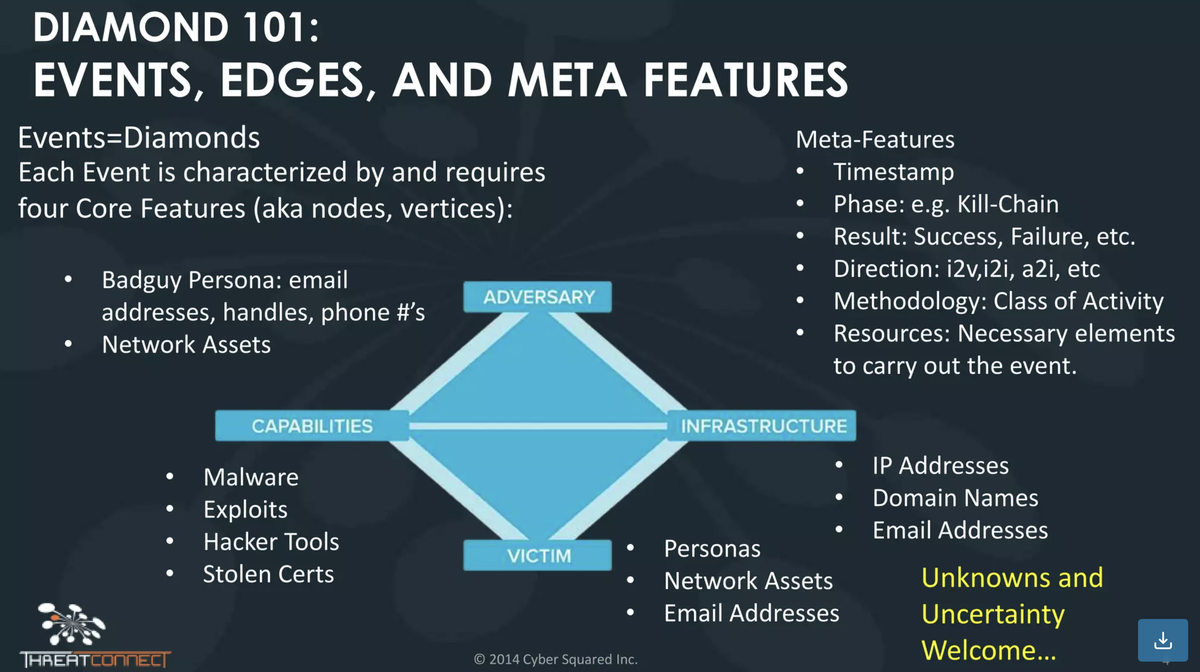
References:
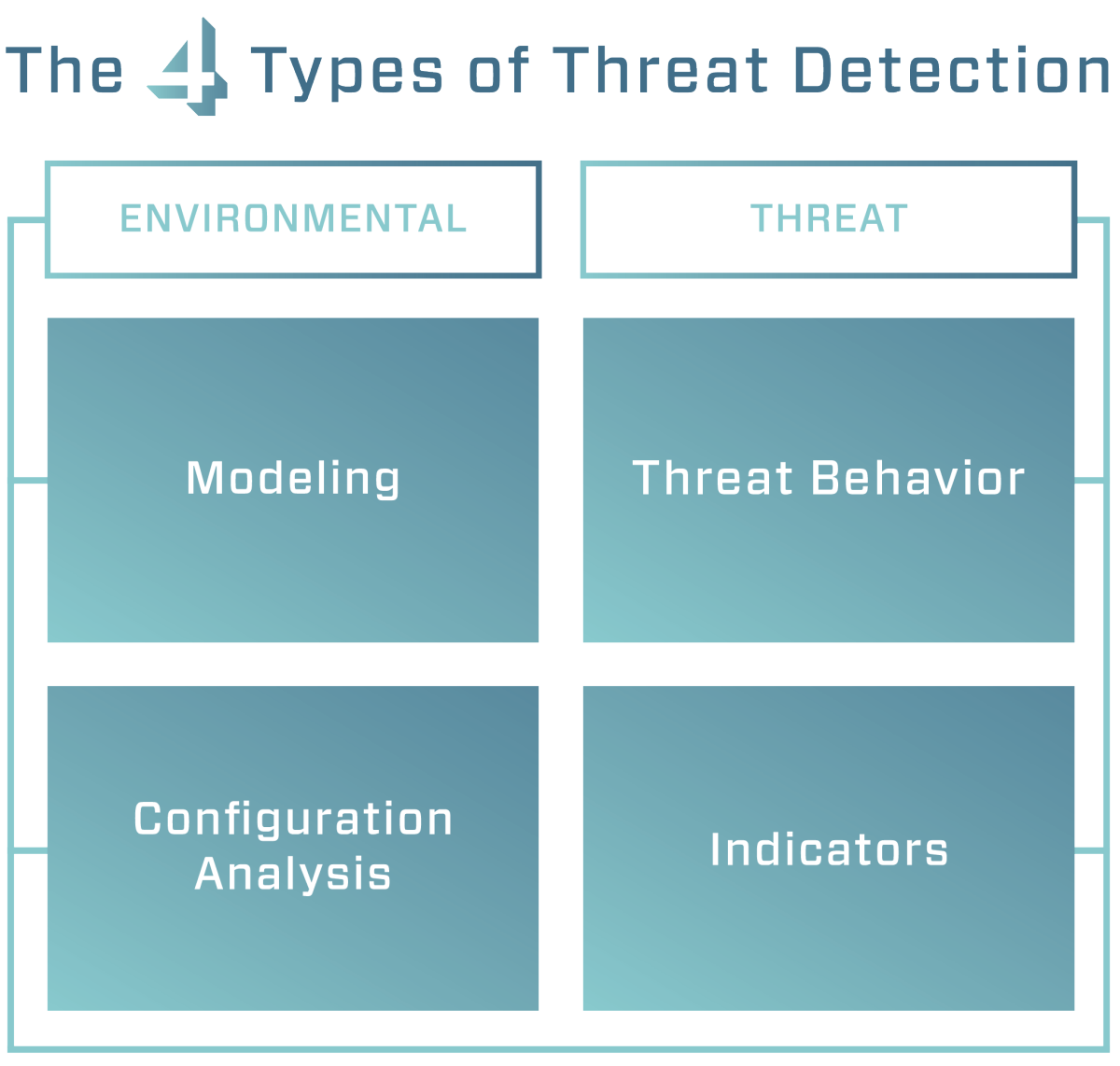
The Four Types of Threat Detection
A model outlining four types of threat detection: signature-based (IOCs), anomaly-based (baselines), behaviour-based (threat behaviour analytics), and reputation-based.
Additional Resources: People Who Said it Better Than Me
In terms of specific resources that would be helpful to someone wanting to move into cybersecurity, Chris Sanders’ training is decent and relatively inexpensive: https://chrissanders.org/training/
Besides that, there’s SANS FOR508, FOR500, and SEC504 certifications (more expensive). You can mitigate some cost by applying for the SANS work-study program: https://www.sans.org/work-study-program/
Additionally, there are many decent books from No Starch Press: https://nostarch.com/
Other than that, these are the things I’d recommend taking a look at.
Training and education
Podcasts
- https://securityweekly.com/
- https://darknetdiaries.com/
- https://isc.sans.edu/podcast.html
- https://cybersecurityinterviews.com/
Books
- Applied Incident Response
- Sandworm
- Countdown to Zero Day
- The Cuckoo’s Egg
- The Phoenix Project
- The Goal
- The Malware Analyst’s Cookbook
- Practical Malware Analysis
And lastly, here are some references I’ve found useful, and still return to from time to time:
- Google Recruiters Say Using the X-Y-Z Formula on Your Resume Will Improve Your Odds of Getting Hired at Google
- A Collection of Resources for Getting Started in ICS/SCADA Cybersecurity
- Starting an InfoSec Career – The Megamix – Chapters 1-3
- So You Want to Learn ICS Security…
In Conclusion
If you made it this far, well done and congratulations 🥳 Hopefully you find this useful.
Let me know if you have any comments, if your experience has been different to mine, or if you think there are considerations that I forgot to mention.
Good luck!