What Is an Alternate Data Stream? NTFS ADS Forensics
Here’s a quick write‑up on Alternate Data Streams (ADS). An ADS is a file attribute used in NTFS that can provide investigators with valuable evidence that might otherwise be overlooked.
Quick Answer: What Is an Alternate Data Stream?
An Alternate Data Stream (ADS) is a named stream attached to an NTFS file or folder. It can hold extra data without changing what the parent file appears to contain in File Explorer or a standard dir listing.
For investigators, ADS matter because they can hide scripts, binaries, documents, or metadata in a place that normal browsing misses. An ADS finding is useful evidence, but it still needs context: who created it, when it changed, whether it executed, and what other artefacts support the same story.
An ADS is an additional named stream of data that a user can attach to a file or folder on Windows systems. It’s effectively hidden data associated with a visible file (or written alongside a regular file) and is not visible in standard file browsers such as File Explorer. The original intent of ADS was to allow files to contain additional metadata or alternate data that’s not part of the primary file content.
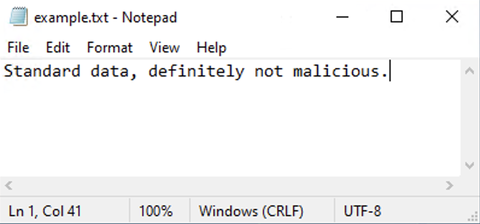
For example, a text file could have an ADS containing comments or supplementary information about that file. That data could be accessed by a specific application or user, but it wouldn’t be displayed as part of the parent file’s visible contents. In practice, however, ADS can store almost any type of data, including scripts, binaries, images, and text documents.
What makes ADS particularly interesting from a forensic perspective is the ability to hide data within a file without changing the file’s size or apparent contents. An adversary could, for example, hide malicious code in an ADS attached to a legitimate file. Likewise, a user could conceal sensitive data in an ADS, although most users are unaware that ADS exist at all. This makes ADS a useful hiding place for artefacts that may still be recoverable during an investigation.
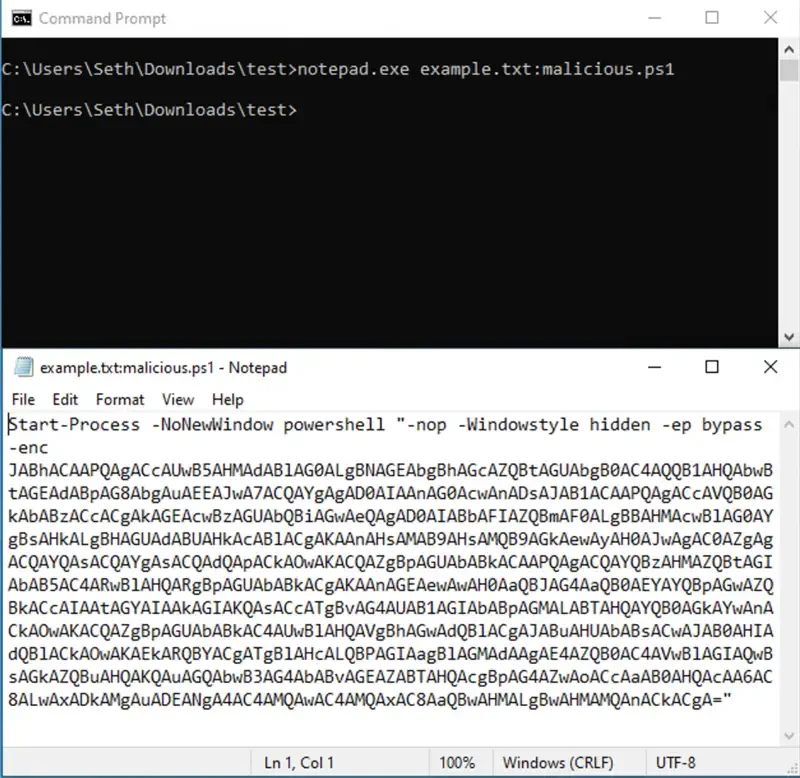
Creating an ADS is usually done from cmd.exe or PowerShell, but it can also be done using Notepad or any other text editor:
notepad.exe example.txt:malicious.ps1
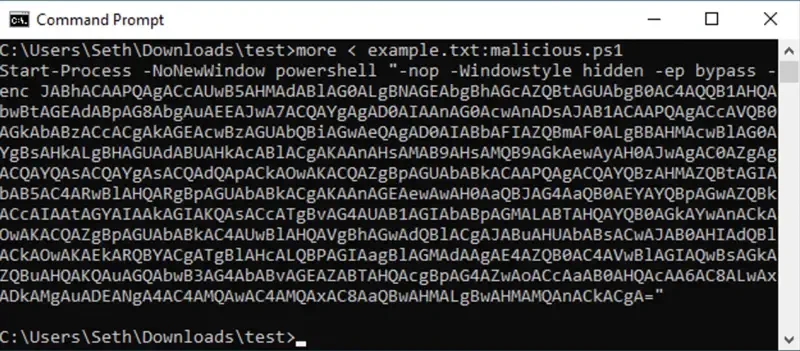
To display the contents of the ADS, use more:
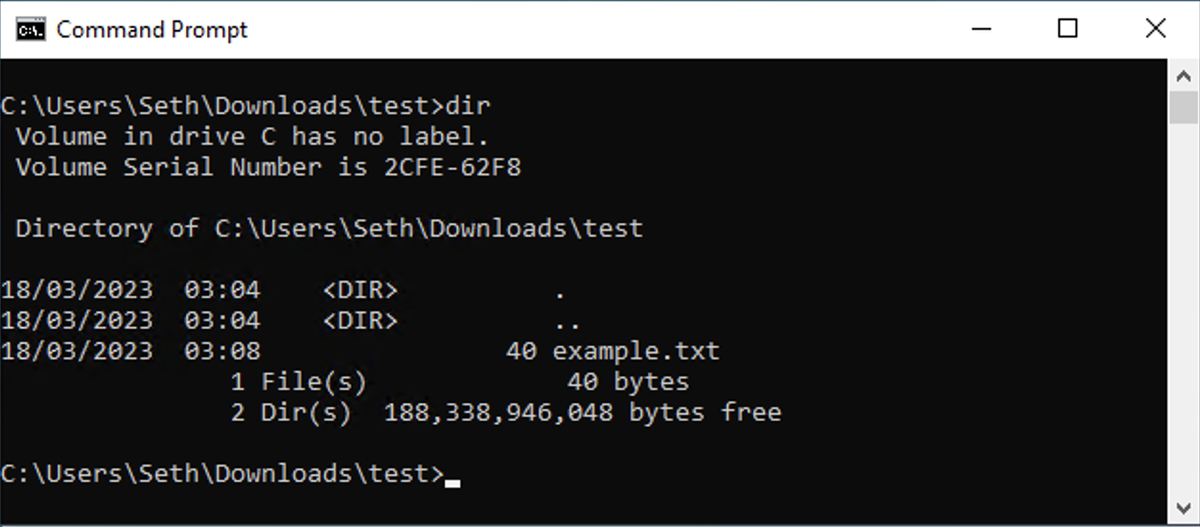
If you list the directory contents using dir, nothing unusual is visible:
However, running dir /r reveals the presence of alternate data streams:
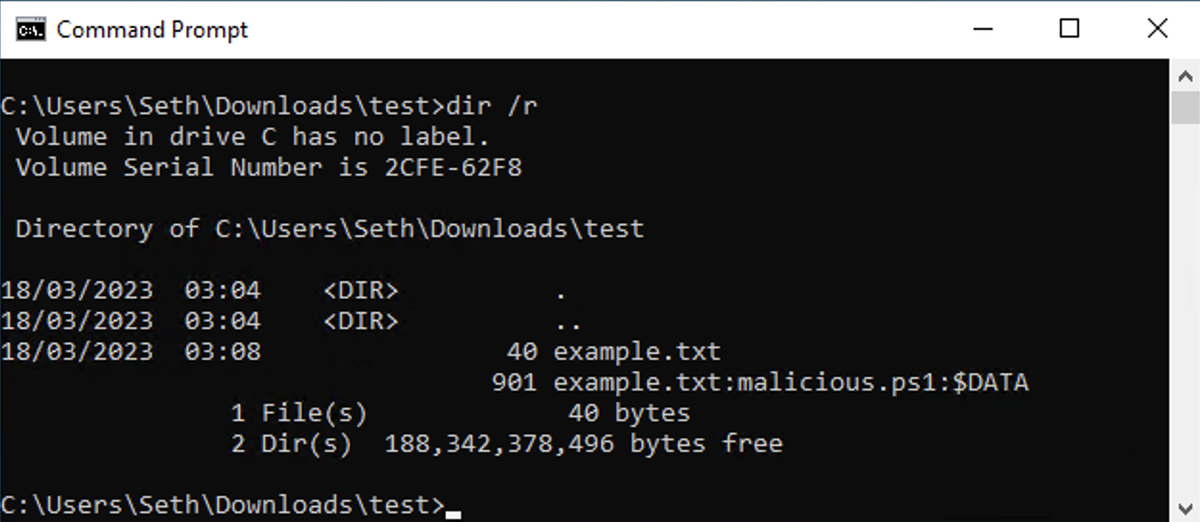
Notice that the size of the parent example.txt file hasn’t changed; all the additional data is stored entirely within the ADS itself.
ADS are a powerful NTFS feature and can be legitimately useful in some scenarios. From a defensive and forensics standpoint, it’s important to remember that executable code or scripts can be stored in ADS and, in some cases, executed directly from the alternate data stream. This makes ADS something worth actively looking for during investigations.
